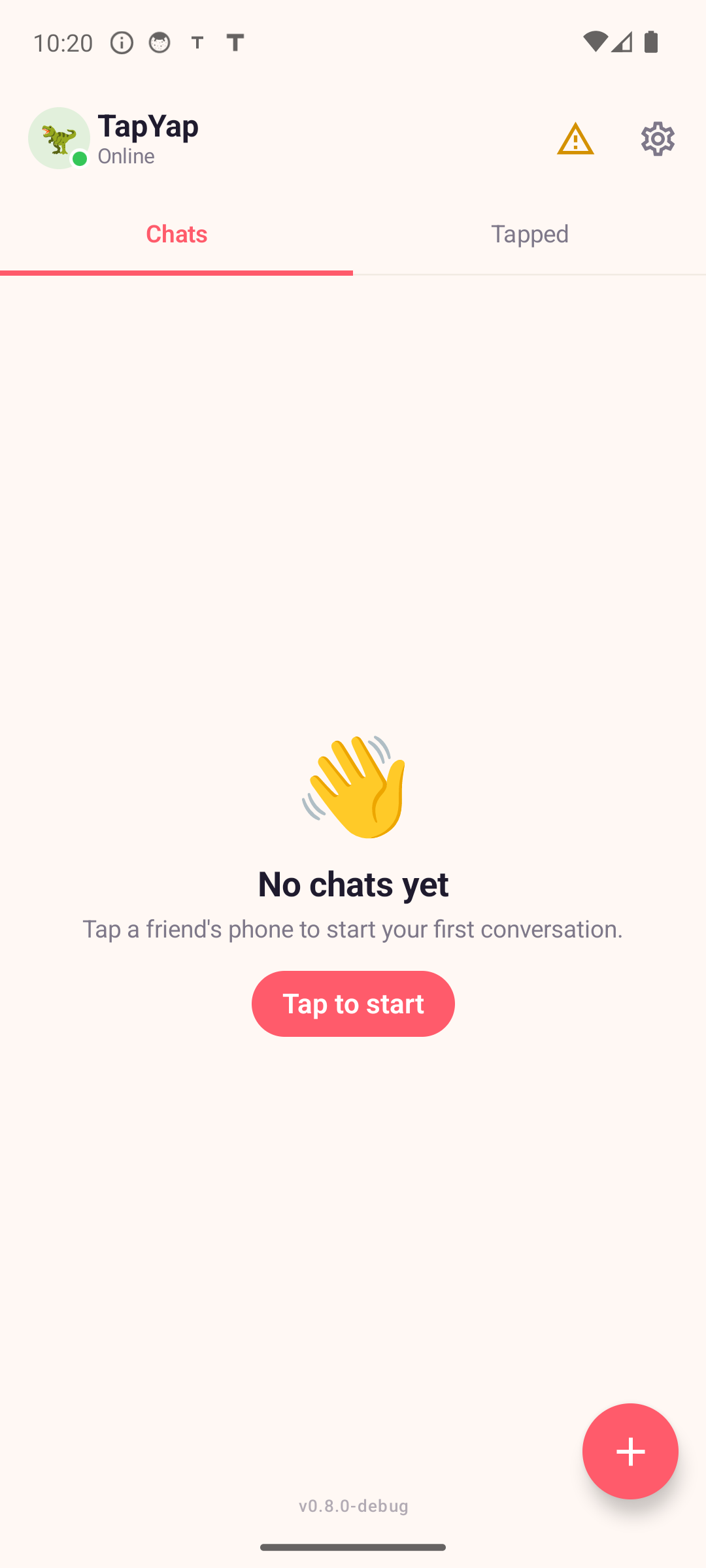
How it works
No sign-up forms, no contact import. You meet someone, you tap phones, you can chat — and so can the friends they've already tapped. It's how introductions used to work, just digital.
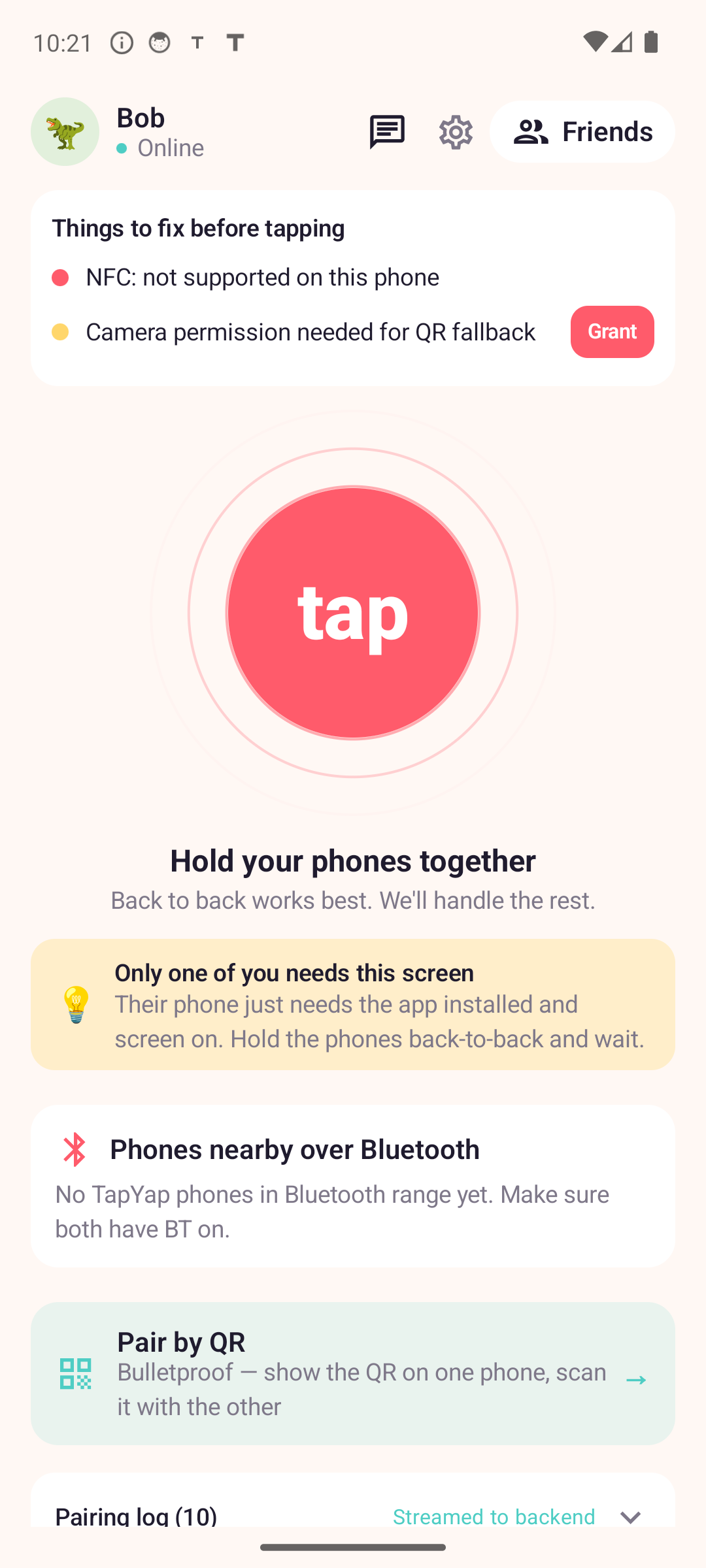
Hold your phones together. NFC does the handshake in under a second — no codes, no QR scans, no "what's your number."
Their face appears in your Tapped tab. You can message them, send photos, share GIFs — same as any chat app.
Anyone they've tapped becomes a friend-of-a-friend you can message too — with attribution showing who introduced you.
Your social graph extends exactly two hops — people you've tapped, and the people they've tapped. No further. No randos. No bots. Real life only.
Why TapYap
Family group chats. Small clubs and crews. Sports teams. The school carpool. Workplace lunch group. Tight, local circles where everyone has met in person — that's the whole point.
Your identity is generated on first launch and lives only on your phone. Never tied to a SIM, an email, or a Big Tech account.
You won't get pinged about your dentist, your high school crush, or anyone you "may know." If you didn't tap them, they're not there.
When Astrid taps Bo, both of your circles see each other — with a clear "via Astrid" label so you know who vouched for them.
Made a tap you regret? Forget Person wipes the connection from your phone. No mutual block lists, no public unfollow.
The real-life-meeting gate means strangers can't reach anyone in your circle. The only way in is a phone someone you trust actually held.
Photos, voice notes, GIFs, group chats, replies, reactions, message edits, disappearing messages. All the basics, none of the friction.
Security
Trust starts in the real world. The cryptography enforces it — not policy. You can chat with people you've physically tapped with, or with someone connected through exactly one tapped friend. The network does not keep expanding forever. Messages stay end-to-end encrypted across servers, offline delivery, and Bluetooth mesh relays. Relays can help move packets, but they do not get the keys.
Every chat relationship is rooted in a physical tap. We don't take strangers' word for who they are; the tap creates a four-signature certificate that cryptographically records the in-person handshake. Your social graph can't grow past two hops — ever — because no one, not even the server, can mint a third.
Provides forward secrecy and post-compromise recovery against both classical and post-quantum adversaries. We default to NIST's Category-5 parameter sets — ML-KEM-1024 for key agreement and ML-DSA-87 for identity signatures — not Category 3, which is what most messengers ship. A session breaks only if both classical (X25519) and lattice (ML-KEM) cryptography fall — not one or the other.
The server stores opaque ciphertexts and signed public keys. It cannot decrypt your messages, mint a tap certificate, or extend a friend-of-friend relationship into broader graph access. The cryptography enforces it, not policy — even a fully compromised server cannot read what you send.
Signal's protocol is the cryptographic gold standard for messaging, and TapYap is built on the same family of primitives. We match Signal on the cryptographic core. Where TapYap goes further is in what it adds on top: physical-tap binding and a hard 2-hop graph ceiling that no other mainstream messenger has shipped.
| Property | TapYap | Signal |
|---|---|---|
| Hybrid post-quantum key agreement (X25519 + ML-KEM lattice) | Yes — ML-KEM-1024 | Yes — ML-KEM-768 |
| Hybrid post-quantum identity signatures (default; Category 5 vs Category 3) | Yes — Ed25519 + ML-DSA-87 | Partial — Ed25519 only |
| Forward secrecy & post-compromise recovery (Double Ratchet) | Yes | Yes |
| End-to-end encrypted media (photos, voice notes, files) | Yes | Yes |
| Cryptographic physical-tap binding for first contact | Yes | No |
| Cryptographic 2-hop social graph ceiling | Yes | No (open graph) |
| Bluetooth mesh transport (works offline) | Yes | No |
| Sealed sender (server can't see who messages whom) | Roadmap | Yes |
| Key transparency / verifiable directory | Roadmap | Rolling out |
| MLS for groups | Roadmap | Rolling out |
| External cryptographic audit completed | Pending | Yes |
| License | Closed-source (commercial-friendly deps) | AGPL-3.0 |
Honesty matters here: Signal has a multi-year head start on operational maturity — their code has been stress-tested by hundreds of millions of users and audited multiple times. We're newer and have an audit pending. The architecture is comparable; the production hardening of the implementation will catch up over time.
Beyond the strong default cryptography, two opt-in modes are available for users with elevated threat models — corporate legal, journalists, activists, dissidents, anyone whose adversary is willing to spend real resources:
We do not have a "maximum security profile" toggle for the cryptographic primitives because we already run the higher-strength NIST parameters by default. Per-message and per-video-frame work uses symmetric encryption (XChaCha20-Poly1305) which is unaffected by post-quantum parameter choice; the only cost of running Category 5 over Category 3 is ~25 ms once per new chat and ~3 KB of one-time bandwidth, both of which are imperceptible. So we just turned it on for everyone.
Live in v0.9.0: paired devices exchange messages end-to-end encrypted via TYSPv1 today — X3DH+PQ session establishment, hybrid Ed25519 / ML-DSA-87 signatures over every prekey, and Double-Ratchet message keys rolling forward on each reply.
Technical detail (TYSPv1): TapYap Secure Protocol v1 uses hybrid X25519 + ML-KEM-1024 key agreement, a Signal-style Double Ratchet with periodic post-quantum re-keying on the roadmap, ChaCha20-Poly1305 authenticated encryption, and hybrid Ed25519 / ML-DSA-87 device identity signatures. Physical taps create four-signature Tap Edge Certificates; friend-of-friend chats use short-lived, non-transitive Introduction Capabilities. Bluetooth mesh packets are opaque encrypted envelopes with rotating route IDs, replay protection, and strict two-hop social limits. Real-time audio/video calls (post-launch) derive SRTP keys from the underlying ratchet so TURN/STUN servers see only encrypted streams.
TYSPv1 is currently in pre-audit review. Once external cryptographic audit is complete, we will publish the audit summary, the full whitepaper, protocol diagrams, and test vectors here. Until then, language on this page describes design intent (“designed to provide”, “post-quantum-hardened”) rather than proven properties. We will also reassess the cryptographic stack against major NIST / IETF updates and emerging post-quantum advancements (including future hybrid-protocol research) as they mature; the wire format includes algorithm-version negotiation so upgrades roll out without breaking existing chats. The full protocol specification and threat model are available in the public repository.
Bonus
When the cell signal disappears — festival crowd, basement venue, plane mode, school WiFi blocked — TapYap quietly switches to a local Bluetooth mesh.
Messages hop phone to phone through nearby friends until they reach their destination. No internet required. The app doesn't tell you to switch modes, and it doesn't make a thing of it — chat just keeps working.